Abstract
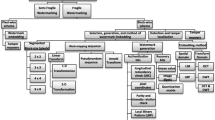
To address the problems of the inferior localization and high probability of false rejection in existing self-recovery fragile watermarking algorithms, this paper proposes a new self-recovery fragile watermarking scheme with superior localization, and further discusses the probability of false rejection (PFR) and the probability of false acceptance (PFA) of the proposed scheme. Moreover, four measurements are defined to evaluate the quality of a recovered image. In the proposed algorithm, the original image is divided into 2×2 blocks to improve localization precision and decrease PFR under occurrence of random tampering. The PFR under occurrence of region tampering can be effectively decreased by randomly embedding the water-mark of each block in conjunction with a novel method of tamper detection. Compared with the current self-recovery fragile watermarking algorithms, the proposed scheme not only resolves the tamper detection problem of self-embedding water-marking, but also improves the robustness against the random tampering of self-embedding watermarking. In addition, the subjective measurements are provided to evaluate the performance of the self-recovery watermarking schemes for image authentication.
Similar content being viewed by others
References
Wu J H, Lin F Z. Image authentication based on digital watermarking. Chn J Comput, 2004, 27(9): 1153–1161
Zhu B B, Swanson M D, Tewfik A H. When seeing isn’t believing. IEEE Signal Process Mag, 2004, 3: 40-49
Wong P W, Memon N. Secret and public key image watermarking schemes for image authentication and ownership verification. IEEE Trans Image Process, 2001, 10(10): 1593–1601
Suthaharan S. Fragile image watermarking using a gradient image for improved localization and security. Pattern Recogn Lett, 2004, 25: 1893–1903
He H J, Zhang J S, Tian L. A fragile watermarking scheme with discrimination of tampers on image or watermark. Acta Elect Sin, 2005, 33(9): 1557–1561
Kundur D, Hatzinakos D. Digital watermarking for telltale tamper proofing and authentication. Proc IEEE. 1999, 87(7): 1167–1180
Wo Y, Han G Q, Zhang B. A new Feature-based image content authentication algorithm. Chin J Comput, 2005, 28(1): 105–112
Fridrich J, Goljan M. Images with self-correcting capabilities. In: Proc ICIP’99. Kobe: IEEE Press, 1999. 25–28
Fridrich J, Goljan M. Protection of Digital Images Using Self Embedding. Symposium on Content Security and Data Hiding in Digital Media. New Jersey Institute of Technology, May 14, 1999
He X F, Huang J F, Zhang P J, et al. A new fragile watermark with self-correcting. J Shanghai Norm Univ, 2004, 33(1): 56–62
Zhang H B, Yang C. Tamper detection and self recovery of image using self-embedding. Acta Elect Sin, 2004, 32(2): 196–199
Wang Y J, Zhao Y, Pan Z X. Reversible watermark with self-recovery and tamper-locating capability. J Harbin Institute of Tech (Suppl), 2007, 38(7): 791–795
Zhang J B, Feng D D, Zhang Y N, et al. Fragile image watermarking with restoration capability. Chin J Comput, 2004, 27(3): 371–376
He H J, Zhang J S. A secure tamper detection and recovery algorithm using self-embedding. J Harbin Institute of Tech (Suppl), 2007, 38(7): 889–893
He H J, Zhang J S. Chaos-based scramble self-embedding watermarking algorithm. J Commun, 2006, 27(7): 80–87
Lin P L, Huang P W, Peng A W. A fragile watermarking scheme for authentication with localization and recovery. In: Proceedings of the IEEE 6th International Symposium on Multimedia Software Engineering (ISMSE’04). Miami, 2004. 399–407
Holliman M, Memon N. Counterfeiting attacks on oblivious block-wise independent invisible watermarking schemes. IEEE Trans Image Proc, 2000, 3(9): 432–441
Fridrich J, Goljan M, Memon N. Cryptanalysis of the Yeung-Mintzer fragile watermarking technique. Elect Imag, 2002, 11(4): 262–274
He H J, Zhang J S, Wang H X. Synchronous counterfeiting attacks on self-embedding watermarking schemes. Intl J Comput Sci Network Sec (IJCSNS), 2006, 6(1B): 251–257
Mao W B, Wang J L, Wu Q H. Modern Cryptography: Theory and Practice. Beijing: Publishing House of Electronics Industry, 2004. 137–163
Li Y Q. The Theory of Probability and Statistics. Beijing: Publishing House of Defenses Industry, 2001. 1–253
He H J, Zhang J S, Tai H M. A wavelet-based fragile watermarking scheme for secure image authentication. Lect Notes Comput Sci, 2006, 4283: 422–432
Author information
Authors and Affiliations
Corresponding author
Additional information
Supported by the Program for New Century Excellent Talents in University of China (Grant No. NCET-05-0794), Southwest Jiaotong University Doctors Innovation Funds (2007), and Application Basic Foundation of Sichuan Province, China (Grant No. 2006 J13-10-5)
Rights and permissions
About this article
Cite this article
He, H., Zhang, J. & Chen, F. A self-recovery fragile watermarking scheme for image authentication with superior localization. Sci. China Ser. F-Inf. Sci. 51, 1487–1507 (2008). https://doi.org/10.1007/s11432-008-0094-1
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11432-008-0094-1