Abstract
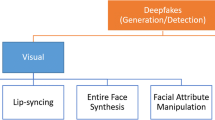
Technologies for producing and modifying content for multimedia have reached to the point that they could now deliver an extremely high degree of realism. Free software tools accessible on the Internet enable anyone with no special expertise to generate incredibly convincing fake images and videos. These technologies provide plenty of new opportunities in various sectors such as fine arts, marketing, film-making, and video games. They could also be employed to influence thoughts of the society in election campaigns, attempt crime, blackmail, or defame individuals. Thus, automated and effective methods of identifying fake media content are urgently needed. This chapter aims to provide an assessment of approaches for validating multimedia integrity as well as detecting modified images and videos. Deepfakes generated using deep learning (DL) techniques will be highlighted particularly, as well as recent data-driven forensics strategies to counter them. The results emphasize the shortcomings of present forensics techniques, the most crucial concerns, emerging obstacles, and future research possibilities.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
Notes
- 1.
Cheapfakes rely on low-cost, easily accessible software or no software at all. They employ standard methods such as slowing, speeding, re-staging, editing, and re-contextualizing footage [39].
References
S. Agarwal, H. Farid, Y. Gu, M. He, K. Nagano, H. Li, Protecting world leaders against deep fakes, in CVPR Workshops, vol. 1 (2019)
C. Barnes, E. Shechtman, A. Finkelstein, D.B. Goldman, PatchMatch: a randomized correspondence algorithm for structural image editing. ACM Trans. Graph. 28(3), 24 (2009)
M. Barni, A. Costanzo, E. Nowroozi, B. Tondi, CNN-based detection of generic contrast adjustment with JPEG post-processing, in 2018 25th IEEE International Conference on Image Processing (ICIP) (2018), pp. 3803–3807. https://doi.org/10.1109/ICIP.2018.8451698
M. Barni, L. Bondi, N. Bonettini, P. Bestagini, A. Costanzo, M. Maggini, B. Tondi, S. Tubaro, Aligned and non-aligned double JPEG detection using convolutional neural networks. J. Vis. Commun. Image Represent. 49, 153–163 (2017)
M. Barni, K. Kallas, E. Nowroozi, B. Tondi, CNN detection of GAN-generated face images based on cross-band co-occurrences analysis, in 2020 IEEE International Workshop on Information Forensics and Security (WIFS) (IEEE, Piscataway, 2020), pp. 1–6
M. Barni, E. Nowroozi, B. Tondi, Higher-order, adversary-aware, double JPEG-detection via selected training on attacked samples, in 2017 25th European Signal Processing Conference (EUSIPCO) (2017), pp. 281–285. https://doi.org/10.23919/EUSIPCO.2017.8081213
M. Barni, E. Nowroozi, B. Tondi, Detection of adaptive histogram equalization robust against JPEG compression, in 2018 International Workshop on Biometrics and Forensics (IWBF) (2018), pp. 1–8
M. Barni, E. Nowroozi, B. Tondi, Improving the security of image manipulation detection through one-and-a-half-class multiple classification. Multimedia Tools Appl. 79(3), 2383–2408 (2020)
B. Biggio, I. Corona, Z.M. He, P.P. Chan, G. Giacinto, D.S. Yeung, F. Roli, One-and-a-half-class multiple classifier systems for secure learning against evasion attacks at test time, in International Workshop on Multiple Classifier Systems (Springer, Berlin, 2015), pp. 168–180
B. Biggio, I. Corona, D. Maiorca, B. Nelson, N. Šrndić, P. Laskov, G. Giacinto, F. Roli, Evasion attacks against machine learning at test time, in Joint European Conference on Machine Learning and Knowledge Discovery in Databases (Springer, Berlin, 2013), pp. 387–402
B. Biggio, G. Fumera, F. Roli, Security evaluation of pattern classifiers under attack. IEEE Trans. Knowl. Data Eng. 26(4), 984–996 (2014)
M. Conti, S. Milani, E. Nowroozi, G. Orazi, Do not deceive your employer with a virtual background: a video conferencing manipulation-detection system. CoRR abs/2106.15130 (2021). https://arxiv.org/abs/2106.15130
D. Cozzolino, L. Verdoliva, Single-image splicing localization through autoencoder-based anomaly detection, in 2016 IEEE International Workshop on Information Forensics and Security (WIFS) (IEEE, Piscataway, 2016), pp. 1–6
Dataset for Real and Virtual Backgrounds of Video Calls. https://zenodo.org/record/5572910. Accessed 28 Mar 2022
T.J. De Carvalho, C. Riess, E. Angelopoulou, H. Pedrini, A. de Rezende Rocha, Exposing digital image forgeries by illumination color classification. IEEE Trans. Inform. Forensics Secur. 8(7), 1182–1194 (2013)
Z. Dias, A. Rocha, S. Goldenstein, Video phylogeny: recovering near-duplicate video relationships, in 2011 IEEE International Workshop on Information Forensics and Security (IEEE, Piscataway, 2011), pp. 1–6
A. Esteva, K. Chou, S. Yeung, N. Naik, A. Madani, A. Mottaghi, Y. Liu, E. Topol, J. Dean, R. Socher, Deep learning-enabled medical computer vision. NPJ Digit. Med. 4(1), 1–9 (2021)
H. Farid, Image forgery detection. IEEE Signal Process. Mag. 26(2), 16–25 (2009)
H. Farid, Photo Forensics (MIT Press, Cambridge, MA, 2016)
A. Ferreira, E. Nowroozi, M. Barni, VIPPrint: validating synthetic image detection and source linking methods on a large scale dataset of printed documents. J. Imaging 7(3), 50 (2021)
M. Fontani, T. Bianchi, A. De Rosa, A. Piva, M. Barni, A framework for decision fusion in image forensics based on Dempster–Shafer theory of evidence. IEEE Trans. Inform. Forensics Secur. 8(4), 593–607 (2013)
T. Gloe, R. Böhme, The’dresden image database’ for benchmarking digital image forensics, in Proceedings of the 2010 ACM Symposium on Applied Computing (2010), pp. 1584–1590
T. Gloe, M. Kirchner, A. Winkler, R. Böhme, Can we trust digital image forensics? in Proceedings of the 15th ACM International Conference on Multimedia (2007), pp. 78–86
D. Güera, S. Baireddy, P. Bestagini, S. Tubaro, E.J. Delp, We need no pixels: video manipulation detection using stream descriptors (2019). arXiv preprint arXiv:1906.08743
H. Huang, P.S. Yu, C. Wang, An introduction to image synthesis with generative adversarial nets (2018). arXiv preprint arXiv:1803.04469
M.K. Johnson, H. Farid, Exposing digital forgeries in complex lighting environments. IEEE Trans. Inform. Forensics Secur. 2(3), 450–461 (2007)
T. Karras, T. Aila, S. Laine, J. Lehtinen, Progressive growing of GANs for improved quality, stability, and variation (2017). arXiv preprint arXiv:1710.10196
E. Kee, J.F. O’Brien, H. Farid, Exposing photo manipulation with inconsistent shadows. ACM Trans. Graph. 32(3), 1–12 (2013)
L. Kennedy, S.F. Chang, Internet image archaeology: automatically tracing the manipulation history of photographs on the web, in Proceedings of the 16th ACM international conference on Multimedia (2008), pp. 349–358
P. Korshunov, S. Marcel, Deepfakes: a new threat to face recognition? Assessment and detection (2018). arXiv preprint arXiv:1812.08685
H. Li, B. Li, S. Tan, J. Huang, Identification of deep network generated images using disparities in color components. Signal Process. 174, 107616 (2020)
L. Li, J. Bao, T. Zhang, H. Yang, D. Chen, F. Wen, B. Guo, Face x-ray for more general face forgery detection, in Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition (2020), pp. 5001–5010
Y. Li, S. Lyu, Exposing deepfake videos by detecting face warping artifacts (2018). arXiv preprint arXiv:1811.00656
J. Lukáš, J. Fridrich, M. Goljan, Detecting digital image forgeries using sensor pattern noise, in Security, Steganography, and Watermarking of Multimedia Contents VIII, vol. 6072 (SPIE, 2006), pp. 362–372
G. Mahfoudi, B. Tajini, F. Retraint, F. Morain-Nicolier, J.L. Dugelay, P. Marc, DEFACTO: image and face manipulation dataset, in 2019 27th European Signal Processing Conference (EUSIPCO) (IEEE, Piscataway, 2019), pp. 1–5
E. Nowroozi, A. Dehghantanha, R.M. Parizi, K.K.R. Choo, A survey of machine learning techniques in adversarial image forensics. Comput. Secur. 100, 102092 (2021)
E. Nowroozi, Y. Mekdad, M. Conti, S. Milani, S. Uluagac, B. Yanikoglu, Real or virtual: a video conferencing background manipulation-detection system (2022). https://arxiv.org/abs/2204.11853
E. Nowroozi, A. Zakerolhosseini, Double jpeg compression detection using statistical analysis. Adv. Comput. Sci. Int. J. 4(3), 70–76 (2015)
B. Paris, J. Donovan, Deepfakes and cheap fakes (2019)
J. Park, D. Cho, W. Ahn, H.K. Lee, Double jpeg detection in mixed JPEG quality factors using deep convolutional neural network, in Proceedings of the European Conference on Computer Vision (ECCV) (2018), pp. 636–652
A. Piva, An overview on image forensics. Int. Scholarly Res. Not. 2013 (2013)
Reuters: Fact check-doctored video appears to show Putin announcing peace (2022). https://www.reuters.com/article/factcheck-putin-address-idUSL2N2VK1CC. Accessed 23 Mar 2022
A. Rossler, D. Cozzolino, L. Verdoliva, C. Riess, J. Thies, M. Nießner, Faceforensics+ +: learning to detect manipulated facial images, in Proceedings of the IEEE/CVF International Conference on Computer Vision (2019), pp. 1–11
E. Sabir, J. Cheng, A. Jaiswal, W. AbdAlmageed, I. Masi, P. Natarajan, Recurrent convolutional strategies for face manipulation detection in videos. Interfaces (GUI) 3(1), 80–87 (2019)
D. Shullani, M. Fontani, M. Iuliani, O. Al Shaya, A. Piva, Vision: a video and image dataset for source identification. EURASIP J. Inform. Secur. 2017(1), 1–16 (2017)
P. Singh, H. Farid, Robust homomorphic image hashing, in CVPR Workshops (2019), pp. 11–18
A. Swaminathan, M. Wu, K.R. Liu, Digital image forensics via intrinsic fingerprints. IEEE Trans. Inform. Forensics Secur. 3(1), 101–117 (2008)
C. Szegedy, W. Zaremba, I. Sutskever, J. Bruna, D. Erhan, I. Goodfellow, R. Fergus, Intriguing properties of neural networks (2013). arXiv preprint arXiv:1312.6199
L. Verdoliva, Media forensics and deepfakes: an overview. IEEE J. Sel. Topics Signal Process. 14(5), 910–932 (2020)
A. Voulodimos, N. Doulamis, A. Doulamis, E. Protopapadakis, Deep learning for computer vision: a brief review. Comput. Intell. Neurosc. 2018 (2018)
Q. Wang, R. Zhang, Double jpeg compression forensics based on a convolutional neural network. EURASIP J. Inform. Secur. 2016(1), 1–12 (2016)
X. Wu, A.G. Hauptmann, C.W. Ngo, Practical elimination of near-duplicates from web video search, in Proceedings of the 15th ACM International Conference on Multimedia (2007), pp. 218–227
X. Yang, Y. Li, H. Qi, S. Lyu, Exposing GAN-synthesized faces using landmark locations, in Proceedings of the ACM Workshop on Information Hiding and Multimedia Security (2019), pp. 113–118
P. Yu, Z. Xia, J. Fei, Y. Lu, A survey on deepfake video detection. IET Biom. 10(6), 607–624 (2021)
P. Zhou, B.C. Chen, X. Han, M. Najibi, A. Shrivastava, S.N. Lim, L. Davis, Generate, segment, and refine: towards generic manipulation segmentation, in Proceedings of the AAAI Conference on Artificial Intelligence, vol. 34 (2020), pp. 13058–13065
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2022 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this chapter
Cite this chapter
Nowroozi, E., Seyedshoari, S., Mohammadi, M., Jolfaei, A. (2022). Impact of Media Forensics and Deepfake in Society. In: Daimi, K., Francia III, G., Encinas, L.H. (eds) Breakthroughs in Digital Biometrics and Forensics. Springer, Cham. https://doi.org/10.1007/978-3-031-10706-1_18
Download citation
DOI: https://doi.org/10.1007/978-3-031-10706-1_18
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-10705-4
Online ISBN: 978-3-031-10706-1
eBook Packages: Computer ScienceComputer Science (R0)