Abstract
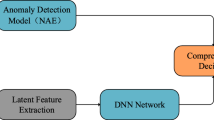
As the accuracy rate of artificial intelligence based applications increased, they have started to be used in different areas. Artifical Neural Networks (ANN) can be very successful for extracting meaningful data from features by processing complex data. Well-trained models can solve difficult problems with high a high accuracy rate. In this study, 2 different ANN models have been developed to detect malicious users who want to access high-security servers. These models are tested from simple to complex: Shallow Neural Network (SNN), Deep Neural Network (DNN), and Auto Encoder are used to reduce features. All models are trained with CICIDS2017 dataset. Server connection requests are classified as normal or malicious (Brute Force, Web Attack, In ltration, Botnet or DDoS) with 98.45% accuracy rate.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Ponemon Institute: 2017 Cost of Data Breach Study: Global Overview, NorthTraverse City, Michigan 49686 USA (2017)
Gyanchandani, M., Rana, J.L., Yadav, R.N.: Taxonomy of anomaly based intrusion detection system: a review. Int. J. Sci. Res. Publ. 2(12), 1–13 (2012)
Shameli-Sendi, A., Ezzati-Jivan, N., Jabbarifar, M., Dagenais, M.: Intrusion response systems: survey and taxonomy. Int. J. Comput. Sci. Netw. Secur. 12(1), 1–14 (2012)
Taylor, D.E.: Survey and taxonomy of packet classification techniques. ACM Comput. Surv. (CSUR) 37(3), 238–275 (2005)
Axelsson, S.: Intrusion detection systems: a survey and taxonomy, vol. 99. Technical report (2000)
Sabahi, F., Movaghar, A.: Intrusion detection: a survey. In: Third International Conference on Systems and Networks Communications, pp. 23–26. IEEE, Sliema (2008)
Diep, N.N.: Intrusion detection using deep neural network. Southeast Asian J. Sci. 5(2), 111–125 (2017)
Roy, S.S., Mallik, A., Gulati, R., Obaidat, M.S., Krishna, P.V.: A deep learning based artificial neural network approach for intrusion detection. In: Giri, D., Mohapatra, R.N., Begehr, H., Obaidat, M.S. (eds.) ICMC 2017. CCIS, vol. 655, pp. 44–53. Springer, Singapore (2017). https://doi.org/10.1007/978-981-10-4642-1_5
Elsherif, A.: Automatic intrusion detection system using deep recurrent neural network paradigm. J. Inf. Secur. Cybercrimes Res. (JISCR) 1, 28–41 (2018). Naif Arab University for Security Sciences
Li, C., Wang, J., Ye, X.: Using a recurrent neural network and restricted Boltzmann machines for malicious traffic detection. NeuroQuantology 16(5), 823–831 (2018). https://doi.org/10.14704/nq.2018.16.5.1391
Kim, J., Shin, N., Jo, S.Y., Kim, S.H.: Method of intrusion detection using deep neural network. In: IEEE International Conference on Big Data and Smart Computing, pp. 313–316 (2017). https://doi.org/10.1109/BIGCOMP.2017.7881684
Karim, A.M., Güzel, M.S., Tolun, M.R., Kaya, H., Çelebi, F.V.: A new generalized deep learning framework combining sparse autoencoder and Taguchi method for novel data classification and processing. In: Mathematical Problems in Engineering (2018). https://doi.org/10.1155/2018/3145947
Jiang, J., et al.: ALDD: a hybrid traffic-user behavior detection method for application layer DDoS. In: 2018 17th IEEE International Conference on Trust, Security and Privacy in Computing and Communications/12th IEEE International Conference on Big Data Science and Engineering (TrustCom/BigDataSE), pp. 1565–1569. IEEE (2018)
Watson, G.: A comparison of header and deep packet features when detecting network intrusions. Digital Repository at the University of Maryland (2018). https://doi.org/10.13016/M2G737680
Sharafaldin, I., Habibi Lashkari, A., Ghorbani, A.A.: Toward generating a new intrusion detection dataset and intrusion traffic characterization. In: Proceedings of the 4th International Conference on Information Systems Security and Privacy (Cic), pp. 108–116 (2018). https://doi.org/10.5220/0006639801080116
Panigrahi, R., Borah, S.: A detailed analysis of CIC2017 dataset for designing Intrusion Detection Systems. Int. J. Eng. Technol. 7, 479–482 (2018)
Ibnkahla, M.: Applications of neural networks to digital communications-a survey. Signal Process. 80(7), 1185–1215 (200)
Liu, W., Wang, Z., Liu, X., Zeng, N., Liu, Y., Alsaadi, F.E.: A survey of deep neural network architectures and their applications. Neurocomputing 234, 11–26 (2017)
Kingma, D.P., Ba, J.: Adam: a method for stochastic optimization. arXiv preprint arXiv:1412.6980 (2014)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2019 Springer Nature Switzerland AG
About this paper
Cite this paper
Ustebay, S., Turgut, Z., Aydin, M.A. (2019). Cyber Attack Detection by Using Neural Network Approaches: Shallow Neural Network, Deep Neural Network and AutoEncoder. In: Gaj, P., Sawicki, M., Kwiecień, A. (eds) Computer Networks. CN 2019. Communications in Computer and Information Science, vol 1039. Springer, Cham. https://doi.org/10.1007/978-3-030-21952-9_11
Download citation
DOI: https://doi.org/10.1007/978-3-030-21952-9_11
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-21951-2
Online ISBN: 978-3-030-21952-9
eBook Packages: Computer ScienceComputer Science (R0)