Abstract
Many software implementations of public key cryptosystems have been concerned with efficiency. The advent of side channel attacks, such as timing and power analysis attacks, force us to reconsider the strategy of implementation of group arithmetic. This paper presents a study of software counter measures against side channel attacks for elliptic curve cryptosystems.
We introduce two new counter measures. The first is a new implementation technique, namely, homogeneous group operations, which has the property that addition and doubling on elliptic curves cannot be distinguished from side channel analysis. Being inexpensive time-wise, this technique is an alternative to a well-known Montgomery ladder. The second is a non-deterministic method of point exponentiation with precomputations. Although requiring rather large ROM, it provides an effective resistance against high-order power analysis attacks for the price of index re-computations and ROM accesses.
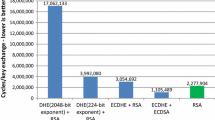
An experimental implementation of NIST-recommended elliptic curves over binary fields with a balanced suite of counter measures built-in in group arithmetic is presented, and the penalty paid is analyzed. The results of the implementation in C on an AMD Duron 600 MHz running Linux are included in the paper.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
ANSI X9.62: The elliptic curve digital signature algorithm (ACDSA), draft, July 1997.
I. Blake, G. Seroussi, N. Smart. Elliptic Curves in Cryptography. Cambridge University Press (1999).
Brier, E., Joye,: Weierstrass elliptic curves and side-channel attacks. Proc. Public Key Cryptography (PKC 2002), LNCS 2274 (2002) 335–345
Brown, M., Hankerson, D., Lopez, J., Menezes, A.: Software implementation of the NIST elliptic curves over prime fields. Proc. CT-RSA 2001, LNCS 2020 (2001) 250–265
Clavier, C., Joye, M.: Universal exponentiation algorithm: A first step towards provable SPA-resistance. Proc. Cryptographic Hardware and Embedded Systems (CHES 2001), LNCS 2162 (2001) 300–308
Chari, S., Jutla, C., Rao, J., Rohatgi, P.: Towards sound approaches to counteract power-analysis attacks. Proc. Advances in Cryptology — Crypto’99, LNCS 1666 (1999) 398–412
Coron, J.-S.: Resistance against differential power analysis attacks for elliptic curve cryptosystems. Proc. Cryptographic Hardware and Embedded Systems (CHES’99), LNCS 1717 (1999) 292–302
Gordon, D. M.: A survey of fast exponentiation methods. J. Algorithms 27 (1998) 129–146
Goubin, L., Patarin, J.: DES and differential power analysis. Proc. Cryptographic Hardware and Embedded Systems (CHES’99), LNCS 1717 (1999) 158–172
Hasan, M. A.: Power analysis attacks and algorithmic approaches to their countermeasures for Koblitz cryptosystems. Proc. Cryptographic Hardware and Embedded Systems (CHES 2000), LNCS 1965 (2000) 93–108
Hankerson, D., Hernandez, J. L., Menezes, A.: Software implementation of elliptic curve cryptography over binary fields. Proc. Cryptographic Hardware and Embedded Systems (CHES 2000), LNCS 1965 (2000)
IEEE Std 1363-2000. IEEE Standard Specification for Public-Key Cryptography. IEEE Computer Society, August 29, 2000
Izu, T., Takagi, T.: A fast parallel elliptic curve multiplication resistant against side channel attacks. Proc. Public Key Cryptography (PKC 2002), LNCS 2274 (2002) 280–296
Joye, M., Quisquater, J-J.,: Hessian elliptic curves and side-channel attacks. Proc. Cryptographic Hardware and Embedded Systems (CHES 2001), LNCS 2162 (2001) 402–410
Joye, M., Tymen, Ch.: Protection against Differential Power Analysis for elliptic curve cryptography — An algebraic approach. Proc. Cryptographic Hardware and Embedded Systems (CHES 2001), LNCS 2162 (2001) 377–390
Joye, M., Yen, S-M.: The Montgomery powering ladder. In these proceedings.
Kocher, P.: Timing attacks on implementations of Diffie-Hellmann, RSA, DSS, and other systems. Proc. Advances in Cryptology — Crypto’96, LNCS 1109 (1996) 104–113
Kocher, P., Jaffe, J., Jun, B.: Differential power analysis. Proc. Advances in Cryptology — Crypto’99, LNCS 1666 (1999) 388–397
Lopez, J., Dahab, R.: Fast multiplication on elliptic curves over GF(2n) without precomputations. Proc. Cryptographic Hardware and Embedded Systems (CHES’99), LNCS 1717 (1999) 316–327
Liardet, P.-Y., Smart, N. P.: Preventing SPA/DPA in ECC systems using the Jacobi form. Proc. Cryptographic Hardware and Embedded Systems (CHES 2001), LNCS 2162 (2001) 391–401
Menezes, A. J., van Oorschot, P. C., Vanstone, S. A.: Handbook in Applied Cryptography. CRC Press, 1997
Messerges, T. S., Dabbish, E. A., Sloan, R. H.: Power analysis attacks on modular exponentiation in smartcards. Proc. Cryptographic Hardware and Embedded Systems (CHES’99), LNCS 1717 (1999)
Messerges, T. S., Dabbish, E. A., Sloan, R. H.: Examining smart-card security under the threat of power analysis attacks. IEEE Transactions on Computers, 51 (5) (2002) 541–552
Montgomery, P.: Speeding the Pollard and elliptic curve methods of factorization. Mathematics of Computations, 48 (1987) 243–264
Okeya, K., Sakaurai, K.: Power analysis breaks Elliptic Curve cryptosystems even secure against the timing attacks. Proc. INDOCRYPT 2000, LNCS 1977 (2000) 178–190
Oswald, E., Aigner, M.: Randomized addition-subtraction chains as a countermeasure against power attacks. Proc. Cryptographic Hardware and Embedded Systems (CHES 2001), LNCS 2162 (2001) 39–50
May, D., Muller, H.L., Smart, N.P.: Non-deterministic processors. Proc. Cryptographic Hardware and Embedded Systems (CHES 2001), LNCS 2162 (2001) 28–38
Yen, S-M., Kim, S-J., Lim, S-G., Moon, S-J: A counter-measure against one physical cryptanalysis may benefit another attack. Proc. Information Security and Cryptology (ICISC 2001), LNCS 2288 (2002) 414–427
De Win,. E., Bosselaers, A., Vandenberghe, S., De Gersem, P., Vandewalle, J.: A fast software implementation for arithmetic operations in GF(2n). Proc. Asiacrypt’ 96, LNCS 1163 (1996) 65–76
De Win,. E., Mister, S., Preneel, B., Wiener M.: On the performance of signature schemes based on elliptic curves. Proc. An Algorithmic Number Theory Symposium, LNCS 1423 (1998)
Woodbury, A., Bailey, D., Paar, Ch.: Elliptic curve cryptography on smart cards without coprocessors. Proc. The Forth Smart Card Research and Advanced Applications Conf., September 20–22, 2000 Bristol, UK
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2003 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Trichina, E., Bellezza, A. (2003). Implementation of Elliptic Curve Cryptography with Built-In Counter Measures against Side Channel Attacks. In: Kaliski, B.S., Koç, ç.K., Paar, C. (eds) Cryptographic Hardware and Embedded Systems - CHES 2002. CHES 2002. Lecture Notes in Computer Science, vol 2523. Springer, Berlin, Heidelberg. https://doi.org/10.1007/3-540-36400-5_9
Download citation
DOI: https://doi.org/10.1007/3-540-36400-5_9
Published:
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-00409-7
Online ISBN: 978-3-540-36400-9
eBook Packages: Springer Book Archive