Abstract
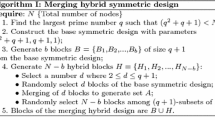
Ad hoc Sensor Networks (ASNs) are ad-hoc mobile networks that consist of sensor nodes with limited computation and communication capabilities. Because ASNs may be deployed in hostile areas, where communication is monitored and nodes are subject to be captured by an adversary, ASNs need a cryptographic protection of communications and sensor-capture detection. According to that the ASN is deployed to carry out some certain tasks, we present a mission-guided key-management scheme. In our scheme, a key ring, which consisting of randomly chosen k keys from a sub-pool of a large offline-generated pool of P keys, is pre-distributed to each sensor node of a group. Compared with Laurent’s scheme, our scheme improves the probability that a shared key exists between two sensor nodes of the same group, and doesn’t affect its security.
Chapter PDF
Similar content being viewed by others
References
Akyildiz, I., Su, W., Sankarasubramaniam, Y., Cayirci, E.: A survey on sensor networks. IEEE Commun. Mag. (August 2002)
Asokan, N., Ginzboorg, P.: Key agreement in ad hoc networks. Comp. Commun. 23, 1627–1637
Zhou, L., Haas, Z.J.: Securing ad hoc networks. IEEE Networks 13(6) (1999)
Kong, J., Zerfos, P., Luo, H., Lu, S., Zhang, L.: Providing robust and ubiquitous security support for mobile ad-hoc networks. In: IEEE ICNP (2001)
Menezes, A., van Oorschot, P., Vanstone, S.: Handbook of Applied Cryptography. CRC Press, Boca Raton (1997) ISBN 0849385237
Hill, J., Szewczyk, R., Woo, A., Hollar, S., Culler, D., Pister, K.: System architecture directions for network sensors. In: Proc. of ASPLOS-IX, Cambridge, Mass. (2000)
Kahn, J.M., Katz, R.H., Pister, K.S.J.: Mobile Networking for Smart Dust. In: ACM/IEEE Intl. Conf. on Mobile Computing and Networking (MobiCom 1999), Seattle, WA, August 17-19, pp. 271–278 (1999)
Carman, D.W., Kruus, P.S., Matt, B.J.: Constraints and Approaches for Distributed Sensor Network Security. Dated September 1, NAI Labs Technical Report #00-010 (2000), Available at http://download.nai.com/products/media/nai/zip/nailabs-report-00-010-final.zip
Gligor, V.D., Donescu, P.: Fast Encryption and Authentication: XCBC Encryption and XECB Authentication Modes. In: Matsui, M. (ed.) FSE 2001. LNCS, vol. 2355, p. 92. Springer, Heidelberg (2002)
Jutla, C.S.: Encryption Modes with Almost Free Message Integrity. In: Pfitzmann, B. (ed.) EUROCRYPT 2001. LNCS, vol. 2045, p. 529. Springer, Heidelberg (2001)
Rogaway, P., Bellare, M., Black, J., Krovetz, T.: OCB: A Block-Cipher Mode of Operations for Efficient Authenticated Encryption. In: Proc. of the 8th ACM Conf. on Computer and Communication Security, Philadelphia, Penn. (November 2001)
Eschenauer, L., Gligor, V.D.: A Key Management Scheme for Distributed Sensor Networks. In: CCS 2002, Washington, DC, USA (November 18-22, 2002)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2004 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Cai, S., Yang, X., Zhao, J. (2004). Mission-Guided Key Management for Ad Hoc Sensor Network. In: Niemegeers, I., de Groot, S.H. (eds) Personal Wireless Communications. PWC 2004. Lecture Notes in Computer Science, vol 3260. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-30199-8_19
Download citation
DOI: https://doi.org/10.1007/978-3-540-30199-8_19
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-23162-2
Online ISBN: 978-3-540-30199-8
eBook Packages: Springer Book Archive