Abstract
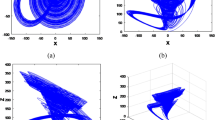
A new three-dimensional (3D) discrete chaotic cipher is proposed which is based on the 3D Lorenz chaotic system. Non-autonomous modulation which is used in continuous chaotic cryptographic systems is employed to encrypt two messages simultaneously. Each pair of data values is encrypted twice so that only one state variable need be transmitted. The proposed algorithm has a simple structure and so is suitable for practical applications. The cryptographic properties are analyzed. Results are presented which show that this algorithm provides excellent security and is resistant to existing attacks such as those based on synchronization.





Similar content being viewed by others
References
Carroll, T.L., Pecora, L.M.: Synchronizing chaotic circuits. IEEE Trans. Circuits Syst. I 38, 453–456 (1991)
Álvarez, G., Li, S.: Some basic cryptographic requirements for chaos-based cryptosystems. Int. J. Bifurc. Chaos 16, 2129–2151 (2006)
Anishchenko, V., Vadivasova, T., Okrokvertskhov, G., Strelkova, G.: Correlation analysis of dynamical chaos. Phys. A Stat. Mech. Appl. 325, 199–212 (2003)
Kocarev, L., Halle, K.S., Eckert, K., Chua, L.O., Parlitz, U.: Experimental demonstration of secure communications via chaotic synchronization. Int. J. Bifurc. Chaos 02, 709–713 (1992)
Álvarez, G., Li, S., Montoya, F., Pastor, G., Romera, M.: Breaking projective chaos synchronization secure communication using filtering and generalized synchronization. Chaos Solitons Fractals 24, 775–783 (2005)
Dedieu, H., Kennedy, M., Hasler, M.: Chaos shift keying: modulation and demodulation of a chaotic carrier using self-synchronizing Chua’s circuits. IEEE Trans. Circuits Syst. II 40, 634–642 (1993)
Yang, T., Yang, L.B., Yang, C.M.: Breaking chaotic switching using generalized synchronization: examples. IEEE Trans. Circuits Syst. I 45, 1062–1067 (1998)
Yang, T., Chua, L.O.: Secure communication via chaotic parameter modulation. IEEE Trans. Circuits Syst. I 43, 817–819 (1996)
Sobhy, M., Shehata, A.: Secure computer communication using chaotic algorithms. Int. J. Bifurc. Chaos 10, 2831–2839 (2000)
Álvarez, G., Montoya, F., Romera, M., Pastor, G.: Breaking parameter modulated chaotic secure communication system. Chaos Solitons Fractals 21, 783–787 (2004)
Zhou, R., Wu, Q., Zhang, M., Shen, C.: Quantum image encryption and decryption algorithms based on quantum image geometric transformations. Int. J. Theor. Phys. 52, 1802–1817 (2013)
Huang, R., Rhee, K., Uchida, S.: A parallel image encryption method based on compressive sensing. Multimed. Tools Appl. 72, 71–93 (2014)
Yong, X., Hua, W., Yongge, L., Bin, P.: Image encryption based on synchronization of fractional chaotic systems. Commun. Nonlinear Sci. Numer. Simul. 19, 3735–3744 (2014)
Xiaoling, H., Guodong, Y.: An image encryption algorithm based on hyper-chaos and DNA sequence. Multimed. Tools Appl. 72, 57–70 (2014)
George, S., Pattathil, D.: A novel approach for secure compressive sensing of images using multiple chaotic maps. J. Opt. 43, 1–17 (2014)
Liu, Z.: Optical color image hiding scheme based on chaotic mapping and Hartley transform. Commun. Opt. Lasers Eng. 51, 967–972 (2013)
Wang, X., Guo, K.: A new image alternate encryption algorithm based on chaotic map. Nonlinear Dyn. 76, 1943–1950 (2014)
Ye, G.: A block image encryption algorithm based on wave transmission and chaotic systems. Nonlinear Dyn. 75, 417–427 (2014)
Lorenz, E.: Deterministic nonperiodic flow. J. Atmos. Sci. 20, 130–141 (1963)
Haroun, M.F., Gulliver, T.A.: New low complexity discrete 3D chaotic generators for communication and security applications. IET Inform. Secur. (submitted)
Schneier, B.: Applied Cryptography: Protocols, Algorithms, and Source Code in C, 2nd edn. Wiley, New York (1996)
Yang, T., Yang, L.B., Yang, C.M.: Cryptanalyzing chaotic secure communications using return maps. Phys. Lett. A 245, 495–510 (1998)
Wu, X., Hu, H., Zhang, B.: Analyzing and improving a chaotic encryption method. Chaos Solitons Fractals 22, 367–373 (2004)
Li, S., Álvarez, G., Chen, G.: Breaking a chaos-based secure communication scheme designed by an improved modulation method. Chaos Solitons Fractals 25, 109–120 (2005)
Orue, A., Álvarez, G., Pastor, G., Romera, M., Montoya, F., Li, S.: A new parameter determination method for some double-scroll chaotic systems and its applications to chaotic cryptanalysis. Commun. Nonlinear Sci. Numer. Simul. 15, 3471–3483 (2010)
Stojanovski, T., Kocarev, L., Parlitz, U.: A simple method to reveal the parameters of the Lorenz system. Int. J. Bifurc. Chaos 6, 2645–2652 (1996)
Solak, E.: Partial identification of Lorenz system and its application to key space reduction of chaotic cryptosystems. IEEE Trans. Circuits Syst. II 51, 557–560 (2004)
Rhouma, R., Meherzi, S., Belghith, S.: OCML-based colour image encryption. Chaos Solitons Fractals 40, 309–318 (2009)
Liu, H., Wang, X.: Color image encryption based on one-time keys and robust chaotic maps. Comput. Math. Appl. 59, 3320–3327 (2010)
Wang, X., Zhao, J., Liu, H.: A new image encryption algorithm based on chaos. Opt. Commun. 285, 562–566 (2012)
Abd El-Latif, A.A., Niu, X.: A hybrid chaotic system and cyclic elliptic curve for image encryption. AEU Int. J. Electron. Commun. 67, 136–143 (2013)
Patidar, V., Pareek, N.K., Purohit, G., Sud, K.K.: A robust and secure chaotic standard map based pseudorandom permutation-substitution scheme for image encryption. Opt. Commun. 284, 4331–4339 (2011)
Sayedzadeh, S.M., Mirzakuchaki, S.: A fast color image encryption algorithm based on coupled two-dimensional piecewise chaotic map. Signal Proc. 92, 1202–1215 (2012)
Chen, G., Mao, Y., Chui, C.K.: A symmetric image encryption scheme based on 3D chaotic cat maps. Chaos Solitons Fractals 21, 749–761 (2004)
Kanso, A., Ghebleh, M.: A novel image encryption algorithm based on a 3D chaotic map. Commun. Nonlinear Sci. Numer. Simul. 17, 2943–2959 (2012)
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Haroun, M.F., Gulliver, T.A. A new 3D chaotic cipher for encrypting two data streams simultaneously. Nonlinear Dyn 81, 1053–1066 (2015). https://doi.org/10.1007/s11071-015-2048-7
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11071-015-2048-7