Abstract
In the contemporary digital era, images are omnipresent, serving as pivotal entities in conveying information, authenticating experiences, and substantiating facts. The ubiquity of image editing tools has precipitated a surge in image forgeries, notably through copy-move attacks where a portion of an image is copied and pasted within the same image to concoct deceptive narratives. This phenomenon is particularly perturbing considering the pivotal role images play in legal, journalistic, and scientific domains, necessitating robust forgery detection mechanisms to uphold image integrity and veracity. While advancements in Convolutional Neural Networks (CNN) have propelled copy-move forgery detection, existing methodologies grapple with limitations concerning the detection efficacy amidst complex manipulations and varied dataset characteristics. Additionally, a palpable void exists in comprehensively understanding and exploiting dataset heterogeneity to enhance detection capabilities. This heralds a pronounced exigency for innovative CNN architectures and nuanced understandings of dataset intricacies to augment detection capabilities, which has remained notably underexplored in the prevailing literature. Against this backdrop, our research broaches novel frontiers in copy-move forgery detection by introducing an innovative CNN architecture meticulously tailored to discern the subtlest manipulations, even amidst intricate image contexts. An extensive analysis of multiple datasets – MICC-F220, MICC-F600, and a combined variant – enables us to delineate a granular understanding of their attributes, thereby shedding unprecedented light on their influences on detection performance. Further, our research goes beyond mere detection, delving deep into comprehensive analyses of varied datasets and conducting additional experiments with differential training-validation sets and randomly labeled data to scrutinize the robustness and reliability of our model. We not only meticulously document and analyze our findings but also juxtapose them against extant models, offering an exhaustive comparative analysis.








Similar content being viewed by others
Data Availability
The data sets generated during and/or analysed during the current study are available from the corresponding author on reasonable request.
References
Amerini I, Anagnostopoulos A, Maiano L, Celsi LR (2021) Deep learning for multimedia forensics. FNT Comput Graph Vision 12:309–457. https://doi.org/10.1561/0600000096
Covello VT (2022) Social media and the changing landscape for risk, high concern, and crisis communication. In: Communicating in risk, crisis, and high stress situations: evidence-based strategies and practice. IEEE, pp 385–410. https://doi.org/10.1002/9781119081753.ch13
Zhu W, Wang X, Gao W (2020) Multimedia intelligence: when multimedia meets artificial intelligence. IEEE Trans Multimed 22:1823–1835. https://doi.org/10.1109/TMM.2020.2969791
Mahmood T, Nawaz T, Irtaza A et al (2016) Copy-move forgery detection technique for forensic analysis in digital images. Math Probl Eng 2016:e8713202. https://doi.org/10.1155/2016/8713202
Team. In: Image and communication laboratory. http://lci.micc.unifi.it/labd/team/. Accessed 22 Jun 2022
Amerini I, Ballan L, Caldelli R, et al (2010) Geometric tampering estimation by means of a SIFT-based forensic analysis. In: 2010 IEEE international conference on acoustics, speech and signal processing, pp 1702–1705. https://doi.org/10.1109/ICASSP.2010.5495485
Amerini I, Ballan L, Caldelli R et al (2011) A SIFT-based forensic method for copy-move attack detection and transformation recovery. IEEE Trans Inf Forensics Secur 6:1099–1110. https://doi.org/10.1109/TIFS.2011.2129512
Elaskily MA, Elnemr HA, Sedik A et al (2020) A novel deep learning framework for copy-moveforgery detection in images. Multimed Tools Appl 79:19167–19192. https://doi.org/10.1007/s11042-020-08751-7
(2022) Next generation cybersecurity systems and applications. In: International scientific conference. http://ngsec.org/. Accessed 22 Jul 2022
Goudelis G, Tefas A, Pitas I (2010) Intelligent multimedia analysis for emerging biometrics. In: Sencar HT, Velastin S, Nikolaidis N, Lian S (eds) Intelligent multimedia analysis for security applications. Springer, Berlin, pp 97–125
Puech W (2022) Multimedia security 2: biometrics, video surveillance and multimedia encryption, 1st edn. Wiley-ISTE, Hoboken
Zeng W, Yu H, Lin C-Y (2006) Multimedia security technologies for digital rights management, 1st edn. Academic Press, Amsterdam
Yahya A (2019) Introduction to steganography. In: Yahya A (ed) Steganography techniques for digital images. Springer International Publishing, Cham, pp 1–7
Singh AK, Kumar B, Singh G, Mohan A (2017) Secure spread spectrum based multiple watermarking technique for medical images. In: Singh AK, Kumar B, Singh G, Mohan A (eds) Medical image watermarking: techniques and applications. Springer International Publishing, Cham, pp 125–157
Fridrich J (2009) Steganography in digital media: principles, algorithms, and applications, illustrated edn. Cambridge University Press, Cambridge
Fkirin A, Attiya G, El-Sayed A, Shouman MA (2022) Copyright protection of deep neural network models using digital watermarking: a comparative study. Multimed Tools Appl 81:15961–15975. https://doi.org/10.1007/s11042-022-12566-z
Vybornova Y (2020) Method for image copyright protection based on construction of highly robust watermarks. In: 2020 8th International symposium on digital forensics and security (ISDFS), pp 1–4. https://doi.org/10.1109/ISDFS49300.2020.9116457
Evsutin O, Melman A, Meshcheryakov R (2020) Digital steganography and watermarking for digital images: a review of current research directions. IEEE Access 8:166589–166611. https://doi.org/10.1109/ACCESS.2020.3022779
Ge M, Persia F (2018) Evaluation in multimedia recommender systems: a practical guide. In: 2018 IEEE 12th International Conference on Semantic Computing (ICSC). pp 294–297
Tang J, Du X, He X et al (2020) Adversarial training towards robust multimedia recommender system. IEEE Trans Knowl Data Eng 32:855–867. https://doi.org/10.1109/TKDE.2019.2893638
Maher RC (2010) Overview of audio forensics. In: Sencar HT, Velastin S, Nikolaidis N, Lian S (eds) Intelligent multimedia analysis for security applications. Springer, Berlin, pp 127–144
Nauman A, Qadri YA, Amjad M et al (2020) Multimedia internet of things: a comprehensive survey. IEEE Access 8:8202–8250. https://doi.org/10.1109/ACCESS.2020.2964280
Kumar M, Jindal MK, Kumar M (2023) An efficient technique for breaking of coloured Hindi CAPTCHA. Soft Comput 27:11661–11686. https://doi.org/10.1007/s00500-023-07844-3
Kumar M, Jindal MK, Kumar M (2022) Design of innovative CAPTCHA for Hindi language. Neural Comput Appl 34:4957–4992. https://doi.org/10.1007/s00521-021-06686-0
Kumar M, Jindal MK, Kumar M (2021) A novel attack on monochrome and greyscale devanagari CAPTCHAs. ACM Trans Asian Low-Resour Lang Inf Process 20:56:1–56:30. https://doi.org/10.1145/3439798
Sencar HT, Verdoliva L, Memon N (2022) Multimedia forensics. Springer, Singapore
Kacprzyk J (2017) Multimedia forensics and security. Springer, Cham
Caldelli R, Amerini I, Ballan L, et al (2012) On the effectiveness of local warping against SIFT-based copy-move detection. In: 2012 5th International symposium on communications, control and signal processing, pp 1–5. https://doi.org/10.1109/ISCCSP.2012.6217846
Amerini I, Ballan L, Caldelli R et al (2013) Copy-move forgery detection and localization by means of robust clustering with J-linkage. Signal Process Image Commun 28:659–669. https://doi.org/10.1016/j.image.2013.03.006
Amerini I, Barni M, Caldelli R, Costanzo A (2013) Counter-forensics of SIFT-based copy-move detection by means of keypoint classification. J Image Video Proc 2013:18. https://doi.org/10.1186/1687-5281-2013-18
Amerini I, Caldelli R, Bimbo AD, et al (2014) Copy-move forgery detection from printed images. In: Media watermarking, security, and forensics 2014. SPIE, pp 336–345. https://doi.org/10.1117/12.2039509
Caldelli R, Amerini I, Costanzo A (2015) SIFT match removal and keypoint preservation through dominant orientation shift. In: 2015 23rd European signal processing conference (EUSIPCO), pp 2062–2066
Hashmi MF, Hambarde A, Anand V, Keskar A (2014) Passive detection of copy-move forgery using wavelet transforms and SIFT features. J Inf Assur Secur (JIAS) 9:197–204
Prajapati BM, Desai NP, Dept E (2015) FORENSIC analysis of digital image tampering. Int J Technol Res Eng 2:5
Warif NBA, Wahab AWA, Idris MYI et al (2016) Copy-move forgery detection: survey, challenges and future directions. J Netw Comput Appl 75:259–278. https://doi.org/10.1016/j.jnca.2016.09.008
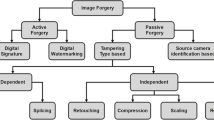
Nabi ST, Kumar M, Singh P et al (2022) A comprehensive survey of image and video forgery techniques: variants, challenges, and future directions. Multimedia Syst 28:939–992. https://doi.org/10.1007/s00530-021-00873-8
Warif NBA, MohdYI I, Wahab AWA et al (2022) A comprehensive evaluation procedure for copy-move forgery detection methods: results from a systematic review. Multimed Tools Appl 81:15171–15203. https://doi.org/10.1007/s11042-022-12010-2
Suresh G, Rao CS (2022) Detection and localization of copy-move forgery in digital images: review and challenges. Int J Image Grap 2350025. https://doi.org/10.1142/S0219467823500250
Elaskily MA, Aslan HK, Elshakankiry OA, et al (2017) Comparative study of copy-move forgery detection techniques. In: 2017 Intl Conf on advanced control circuits systems (ACCS) systems & 2017 Intl Conf on new paradigms in electronics & information technology (PEIT), pp 193–203. https://doi.org/10.1109/ACCS-PEIT.2017.8303041
Ye W, Zeng Q, Peng Y et al (2022) A two-stage detection method of copy-move forgery based on parallel feature fusion. EURASIP J Wirel Commun Netw 2022:30. https://doi.org/10.1186/s13638-022-02112-8
Niu P, Wang C, Chen W et al (2021) Fast and effective keypoint-based image copy-move forgery detection using complex-valued moment invariants. J Vis Commun Image Represent 77:103068. https://doi.org/10.1016/j.jvcir.2021.103068
Chaitra B, Bhaskar Reddy PV (2023) An approach for copy-move image multiple forgery detection based on an optimized pre-trained deep learning model. Knowledge-Based Systems 269:110508. https://doi.org/10.1016/j.knosys.2023.110508
Gan Y, Zhong J, Vong C (2022) A novel copy-move forgery detection algorithm via feature label matching and hierarchical segmentation filtering. Inf Process Manage 59:102783. https://doi.org/10.1016/j.ipm.2021.102783
Yang J, Liang Z, Gan Y, Zhong J (2021) A novel copy-move forgery detection algorithm via two-stage filtering. Digit Signal Process 113:103032. https://doi.org/10.1016/j.dsp.2021.103032
Ganeshan R, Muppidi S, Thirupurasundari DR, Kumar BS (2022) Autoregressive-elephant herding optimization based generative adversarial network for copy-move forgery detection with interval type-2 fuzzy clustering. Signal Process Image Commun 108:116756. https://doi.org/10.1016/j.image.2022.116756
Wang X, Chen W, Niu P, Yang H (2022) Image copy-move forgery detection based on dynamic threshold with dense points. J Vis Commun Image Represent 89:103658. https://doi.org/10.1016/j.jvcir.2022.103658
Kumar S, Gupta SK, Kaur M, Gupta U (2022) VI-NET: a hybrid deep convolutional neural network using VGG and inception V3 model for copy-move forgery classification. J Vis Commun Image Represent 89:103644. https://doi.org/10.1016/j.jvcir.2022.103644
Nazir T, Nawaz M, Masood M, Javed A (2022) Copy move forgery detection and segmentation using improved mask region-based convolution network (RCNN). Appl Soft Comput 131:109778. https://doi.org/10.1016/j.asoc.2022.109778
Gani G, Qadir F (2020) A robust copy-move forgery detection technique based on discrete cosine transform and cellular automata. J Inf Secur Appl 54:102510. https://doi.org/10.1016/j.jisa.2020.102510
Aria M, Hashemzadeh M, Farajzadeh N (2022) QDL-CMFD: a quality-independent and deep learning-based copy-move image forgery detection method. Neurocomputing 511:213–236. https://doi.org/10.1016/j.neucom.2022.09.017
Alhaidery MMA, Taherinia AH, Shahadi HI (2023) A robust detection and localization technique for copy-move forgery in digital images. J King Saud Univ Comput Inf Sci 35:449–461. https://doi.org/10.1016/j.jksuci.2022.12.014
Aydın Y (2022) A new copy-move forgery detection method using LIOP. J Vis Commun Image Represent 89:103661. https://doi.org/10.1016/j.jvcir.2022.103661
Warif NBAbd, Wahab AWA, Idris MohdYI et al (2017) SIFT-symmetry: a robust detection method for copy-move forgery with reflection attack. J Vis Commun Image Represent 46:219–232. https://doi.org/10.1016/j.jvcir.2017.04.004
Dixit A, Bag S (2021) A fast technique to detect copy-move image forgery with reflection and non-affine transformation attacks. Expert Syst Appl 182:115282. https://doi.org/10.1016/j.eswa.2021.115282
(2020) Intuition of adam optimizer. In: GeeksforGeeks. https://www.geeksforgeeks.org/intuition-of-adam-optimizer/. Accessed 25 Jun 2022
Pauls A (2022) Image-forgery. https://github.com/raurica/Image-Forgery
Zhang C, Bengio S, Hardt M et al (2017) Understanding deep learning requires rethinking generalization. https://doi.org/10.48550/arXiv.1611.03530
Acknowledgements
We would like to express our deepest gratitude to Alexandra Pauls, our programmer, who played a pivotal role in conducting the experiments and uploading the source code of the software implementation to GitHub. Her dedication and expertise were invaluable to the success of this work.
Funding
1. This project has received funding from the European Union’s Horizon 2020 research and innovation programme under the Marie Skłodowska-Curie grant agreement No. 101007820-TRUST.
2. This publication reflects only the author’s view and the REA is not responsible for any use that may be made of the information it contains.
Author information
Authors and Affiliations
Contributions
• Conceptualization and methodology, writing-review and editing, Alexandr Kuznetsov;
• Formal analysis, investigation, Emanuele Frontoni;
• Resources, Luca Romeo;
• Data curation, Riccardo Rosati;
• All authors have read and agreed to the published version of the manuscript.
Corresponding author
Ethics declarations
Competing interests
The authors have no competing interests to declare that are relevant to the content of this article.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Kuznetsov, O., Frontoni, E., Romeo, L. et al. Enhancing copy-move forgery detection through a novel CNN architecture and comprehensive dataset analysis. Multimed Tools Appl 83, 59783–59817 (2024). https://doi.org/10.1007/s11042-023-17964-5
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-023-17964-5