Abstract
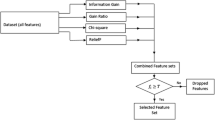
The contributions of this paper are threefold—(i) to provide a detailed analysis of two benchmark datasets CIDDS-001 and CICIDS-2017, (ii) to evaluate three prominent feature ranking methods and to quantify the closeness factor between the features and the class label through statistical analysis, and (iii) to evaluate the performance of different traditional classifiers on cloud environment using these datasets. These datasets are generated on cloud environment which contains contemporary attacks. These contributions will provide a prior knowledge to the defenders for building an ideal NIDS with selection of suitable algorithms for feature learning and classification. Machine learning and dimensionality reduction algorithms are applied by many researchers with the lack of knowledge about which algorithm is suitable to get good performance. Having prior knowledge of the dataset structure and statistical behavior of various features will help in implementing the suitable algorithms to obtain maximum detection rates with minimum computational time. To fulfil this task and to achieve the above-mentioned contributions, the experiments are carried out. Finally, the results are presented and conclusions are drawn.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Garcia-Teodoro P, Diaz-Verdejo J, Maciá-Fernández G, Vázquez E (2009) Anomaly-based network intrusion detection: techniques, systems and challenges. Comput Security 28(1–2):18–28
Modi C, Patel D, Borisanya B, Patel A, Rajarajan M (2012) A novel framework for intrusion detection in cloud. In: Proceedings of the fifth international conference on security of information and networks, pp 67–74
Mahmood HA (2018) Network intrusion detection system (NIDS) in cloud environment based on hidden Naïve Bayes multiclass classifier. Al-Mustansiriyah J Sci 28(2):134–142
Gharib A, Sharafaldin I, Lashkari AH, Ghorbani AA (2016) An evaluation framework for intrusion detection dataset. In: International Conference on Information Science and Security (ICISS) IEEE, pp 1–6
Villacampa O (2015) Feature selection and classification methods for decision making: a comparative analysis. PhD thesis, College of Engineering and Computing, Nova Southeastern University
Karegowda AG, Manjunath AS, Jayaram MA (2010) Comparative study of attribute selection using gain ratio and correlation based feature selection. Int J Information Technol Knowl Manage 2(2):271–277
CICIDS (2017) https://www.unb.ca/cic/datasets/ids-2017.html
Stiawan D et al (2020) CICIDS-2017 dataset feature analysis with information gain for anomaly detection. IEEE Access 8:132911–132921
Khoshgoftaar TM, Gao K, Napolitano A (2012) An empirical study of feature ranking techniques for software quality prediction. Int J Software Eng Knowl Eng 22(02):161–183
Zdravevski E, Lameski P, Kulakov A, Jakimovski B, Filiposka S, Trajanov D (2015) Feature ranking based on information gain for large classification problems with mapreduce. IEEE Trustcom/BigDataSE/ISPA 2:186–191
Statistical Analysis 2018. https://www.statsref.com/StatsRefSample.pdf
Rao BB, Swathi K (2017) Fast kNN classifiers for network intrusion detection system. Indian J Sci Technol 10(14):1–10
Swathi K, Rao BB (2019) Impact of PDS based kNN classifiers on Kyoto dataset. Int J Rough Sets Data Anal (IJRSDA) 6(2):61–72
Wang W, Du D, Wang N (2018) Building a cloud IDS using an efficient feature selection method and SVM. IEEE Access 7:1345–1354
Safaldin M, Otair M, Abualigah L (2020) Improved binary gray wolf optimizer and SVM for intrusion detection system in wireless sensor networks. J Ambient Intelligence Humanized Comput 1–18
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2022 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Vamsi Krishna, K., Swathi, K., Rama Koteswara Rao, P., Basaveswara Rao, B. (2022). A Detailed Analysis of the CIDDS-001 and CICIDS-2017 Datasets. In: Ranganathan, G., Bestak, R., Palanisamy, R., Rocha, Á. (eds) Pervasive Computing and Social Networking. Lecture Notes in Networks and Systems, vol 317. Springer, Singapore. https://doi.org/10.1007/978-981-16-5640-8_47
Download citation
DOI: https://doi.org/10.1007/978-981-16-5640-8_47
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-16-5639-2
Online ISBN: 978-981-16-5640-8
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)