Abstract
Secure audio teleconferencing is a multi-point communication service which uses encryption to prevent eavesdroppers from listening to the speech signals. Its greatest vulnerability is the audio bridge — that component which combines the conferees’ speech signals and returns the result to them.
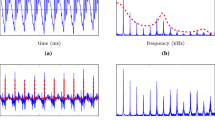
A new secure teleconferencing system is proposed here. It fits the public telephone network by eliminating the need for the conferees to share their secrets with the bridge. It combines a simplified (‘instantaneous’) bridging technique with secure bridging ideas previously suggested in the literature, overcoming their main practical disadvantages. In particular, it is not restricting the audio signals to be coded by linear PCM, a technique which is wasteful in terms of bit-rate. Rather, it enables the use of conventional μ-law and A-law PCM, as well as vector quantized PCM, thus can be used with a conventional 64kb/s digital channel.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
E.F. Brickell, P.J. Lee, and Y. Yacobi. Secure audio teleconference, volume 293 of Lecture notes in computer science: Advances in cryptology — CRYPTO’ 87, pages 418–426. Springer-Verlag, 1987.
International Telegraph and Telephone Consultative Committee. Pulse Code Modulation (PCM) of voice frequencies. CCITT recommendation G.711, Geneva, 1972.
International Telegraph and Telephone Consultative Committee. Frame structure for a 64 to 1920 kbit/s channel in audiovisual systems, 1990. CCITT recommendation H.221.
J.M. Carrol and S. Martin. The automated cryptanalysis of substitution ciphers. Cryptologia, 10:193–209, 1986.
J.M. Carrol and L.E. Robbins. The automated cryptanalysis of polyalphabetic ciphers. Cryptologia, 11:193–205, 1987.
The National Bureau of Standards. Data Encryption Standard, January 1977. U.S. department of Commerce, FIPS pub. 46.
B. Goldburg, E. Dawson, and S. Sridharan. The automated cryptanalysis of analog speech scramblers. In Advances in Cryptology, Eurocrypt, pages 422–430, 1991.
N.S. Jayant and P. Noll. Digital coding of waveforms: principles and applications to speech and video. Prentice-Hall Inc., Englewood Cliffs, N.J., 1984.
J.L. Massey. private communication.
Electrospace Systems Inc. MDS-1 video conferencing bridge, manuscript. Mail stop 4000, p.o.box 831359, Richardson, Texas 75083-1359, 1991.
J. Makhoul, S. Roucos, and H. Gish. Vector quantization in speech coding. Proc. of the IEEE, 73(11), November 1985.
M. V. Pitke and T. Chandrasekaran. An improved conference circuit. Proc. of IEEE, 71(12):1460–1461, 1983.
M. V. Pitke and T. Chandrasekaran. A digital conferencing technique. Proc. of IEEE, 73(11):1687–1688, 1985.
S. G. Pitroda and B. J. Rekiere. A digital conference circuit for an instant speaker algorithm. IEEE transactions on communication technology, com-19(6):1069–1076, December 1971.
L.R. Rabiner and R.W. Schafer. Digital processing of speech signals. Prentice-Hall, 1979.
R. Rivest, A. Shamir, and L. Adelman. A method for obtaining digital signatures and public-key cryptosystems. Communications of the ACM, 21:120–126, 1978.
A. Shimizu and S. Miyaguchi. Fast data encryption algorithm (FEAL). In Advances in Cryptology, Eurocrypt, pages 267–267, 1987.
D.G. Steer, L. Strawczynski, W. Diffie, and M. Wiener. A secure audio teleconference system, volume 403 of Lecture notes in computer science: Advances in cryptology — CRYPTO’ 88, pages 520–528. Springer-Verlag, 1988.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 1993 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Heiman, R. (1993). Secure Audio Teleconferencing: A Practical Solution. In: Rueppel, R.A. (eds) Advances in Cryptology — EUROCRYPT’ 92. EUROCRYPT 1992. Lecture Notes in Computer Science, vol 658. Springer, Berlin, Heidelberg. https://doi.org/10.1007/3-540-47555-9_36
Download citation
DOI: https://doi.org/10.1007/3-540-47555-9_36
Published:
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-56413-3
Online ISBN: 978-3-540-47555-2
eBook Packages: Springer Book Archive